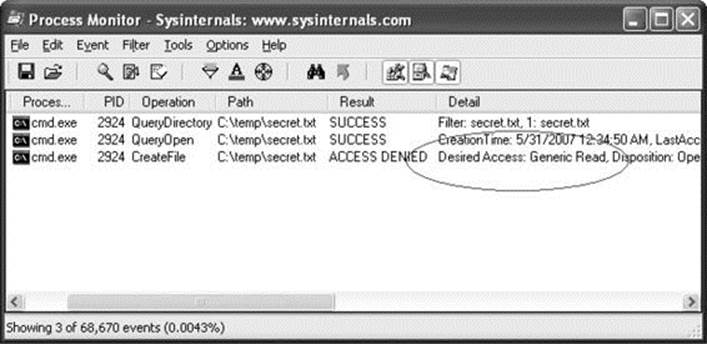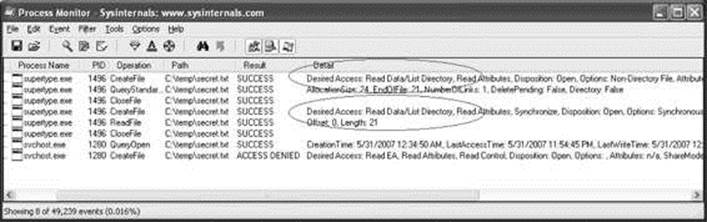
Exploiting the Windows Access Control Model - From Vulnerability to Exploit - Praise for Gray Hat Hacking: The Ethical Hacker's Handbook, Fourth Edition (2015)
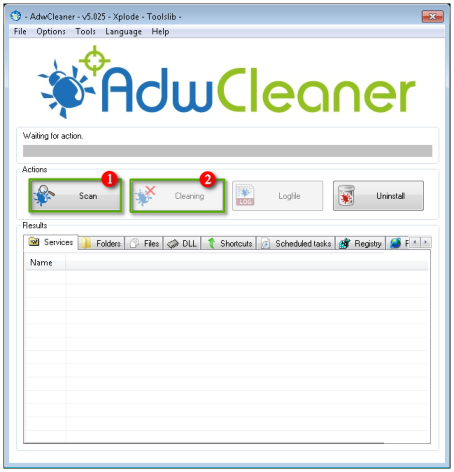
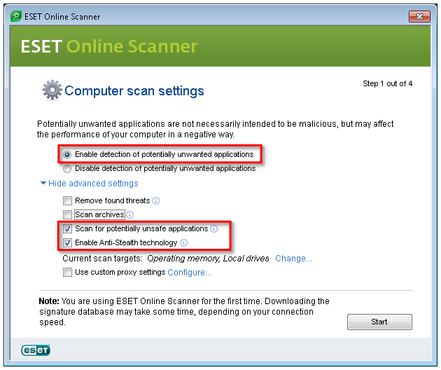
Tricky virus/malware Windows Process Manager. Please help - Resolved Malware Removal Logs - Malwarebytes Forums

Trying to connect to an Ms Access Db and I don't have admin rights or ACE.OLEDB.16.0 - Stack Overflow
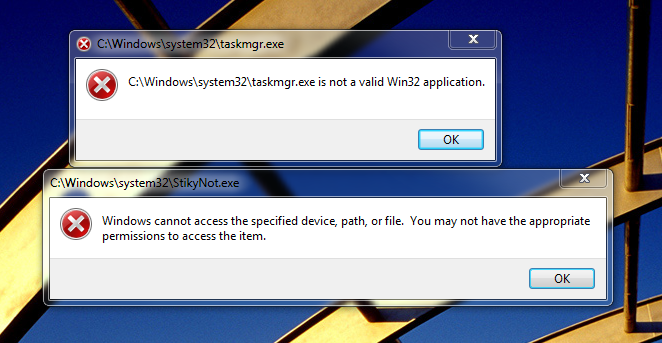
system32\taskmgr.exe is not a valid win32 application." - Virus, Trojan, Spyware, and Malware Removal Help

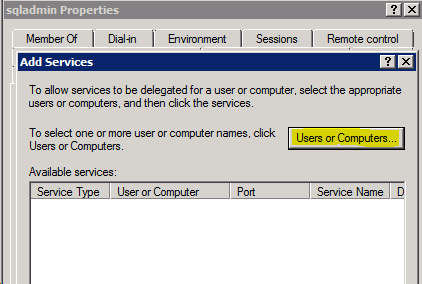
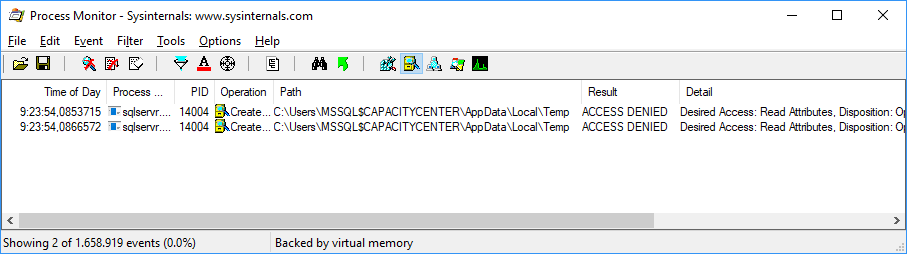
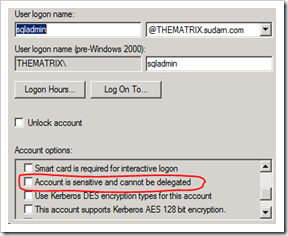
SQL SERVER - SQL Server Agent Not Starting - Failed to Initialize SQL Agent Log (Reason: Access is Denied). - SQL Authority with Pinal Dave